Overview
Cryptographically secure file sharing that stays safe under full storage compromise
A secure file-sharing web app that encrypts data before storage and verifies integrity before decryption. Built to remain confidential even if the storage layer is fully breached — using the same cryptographic controls found in production security systems.
Technical Deep-Dive
Built a Flask-based system enforcing a verify-then-decrypt model to eliminate decryption oracle risks (aligned with OWASP cryptographic best practices). Implements AES-256-GCM (NIST SP 800-38D) for authenticated encryption, RSA-OAEP / RSA-PSS (RFC 8017) for secure key transport and digital signatures, and ECDH P-256 + HKDF (RFC 5869) to achieve Perfect Forward Secrecy — mirroring the TLS 1.3 key exchange model.
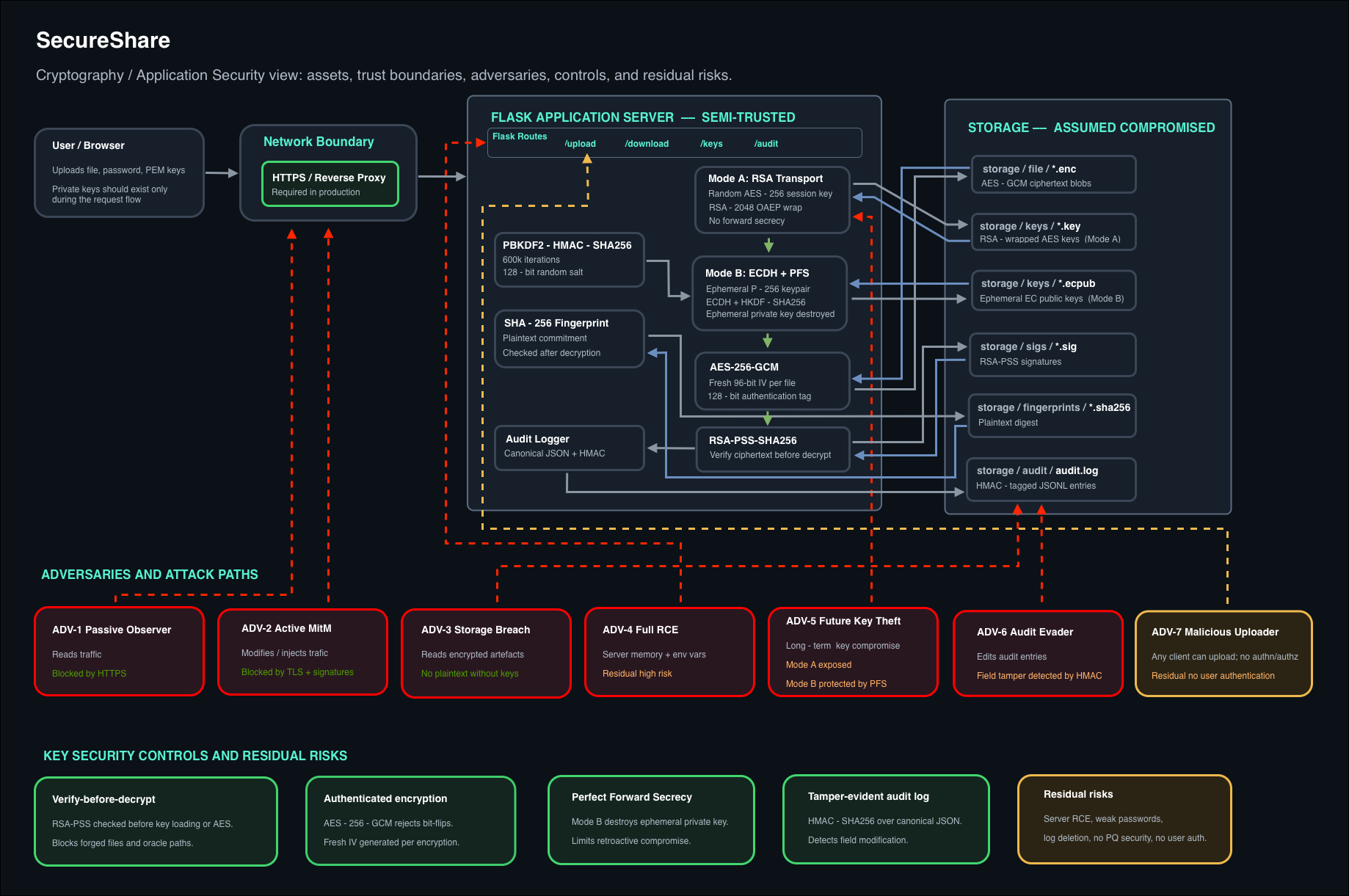
The architecture assumes a compromised storage layer, ensuring confidentiality under full read access. Every operation is logged in a tamper-evident HMAC-SHA256 audit trail (RFC 2104) — enabling detection of unauthorised modifications and satisfying a core SOC visibility requirement.
Impact & Metrics
- Engineered dual encryption modes (RSA key transport + ECDH PFS), demonstrating real-world trade-offs between long-term key exposure and forward secrecy across documented attack scenarios.
- Validated cryptographic guarantees with 83 unit tests covering tamper detection, key misuse, IV reuse, signature forgery, and forward secrecy failure conditions.
- Designed a storage-compromise-resilient architecture enforcing signature verification before any decryption path — stress-tested against four simulated adversarial attack classes.
Code / Test Screenshot
verify-then-decrypt function or pytest output showing 83 passing tests
Dark theme · Carbon (carbon.now.sh) or ray.so recommended