Evanildo Ribeiro
SOC Analyst & Security Engineer | AI Security Research
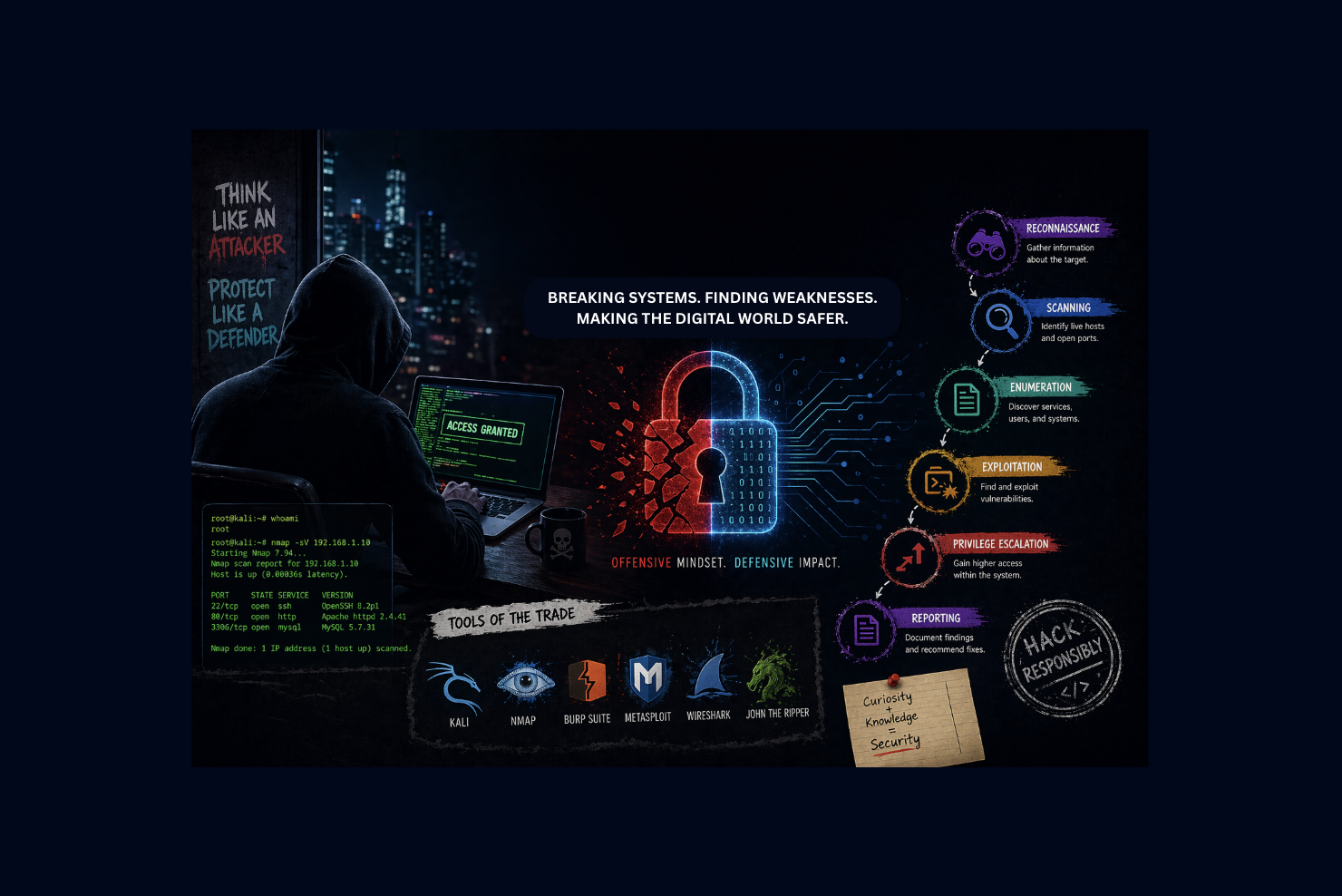
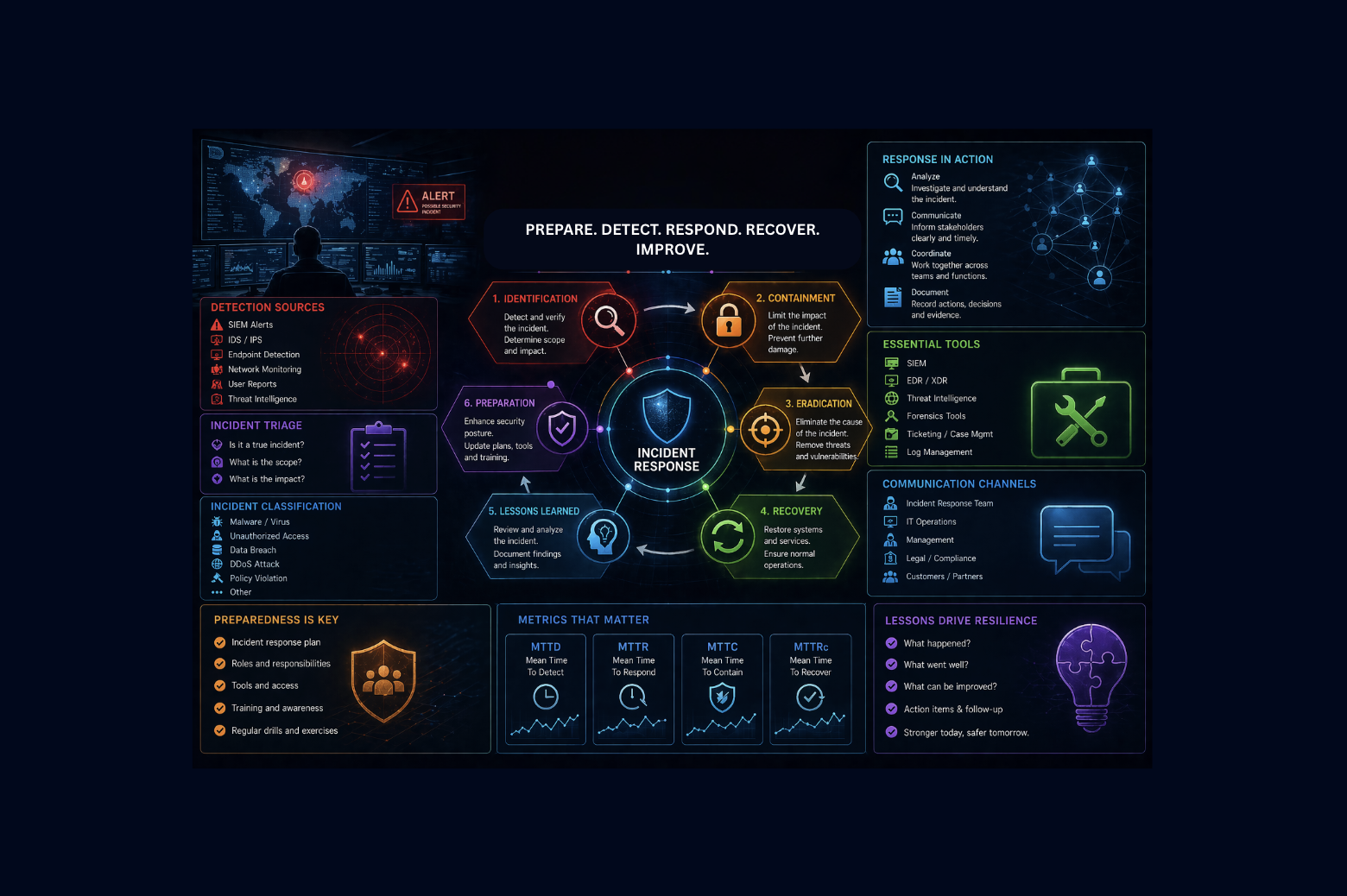
SOC Analyst and Security Engineer with proven experience in defensive security operations, research-driven threat analysis, and applied incident response. I combine a strong technical foundation with a proactive mindset to detect, analyse, and respond to security events.
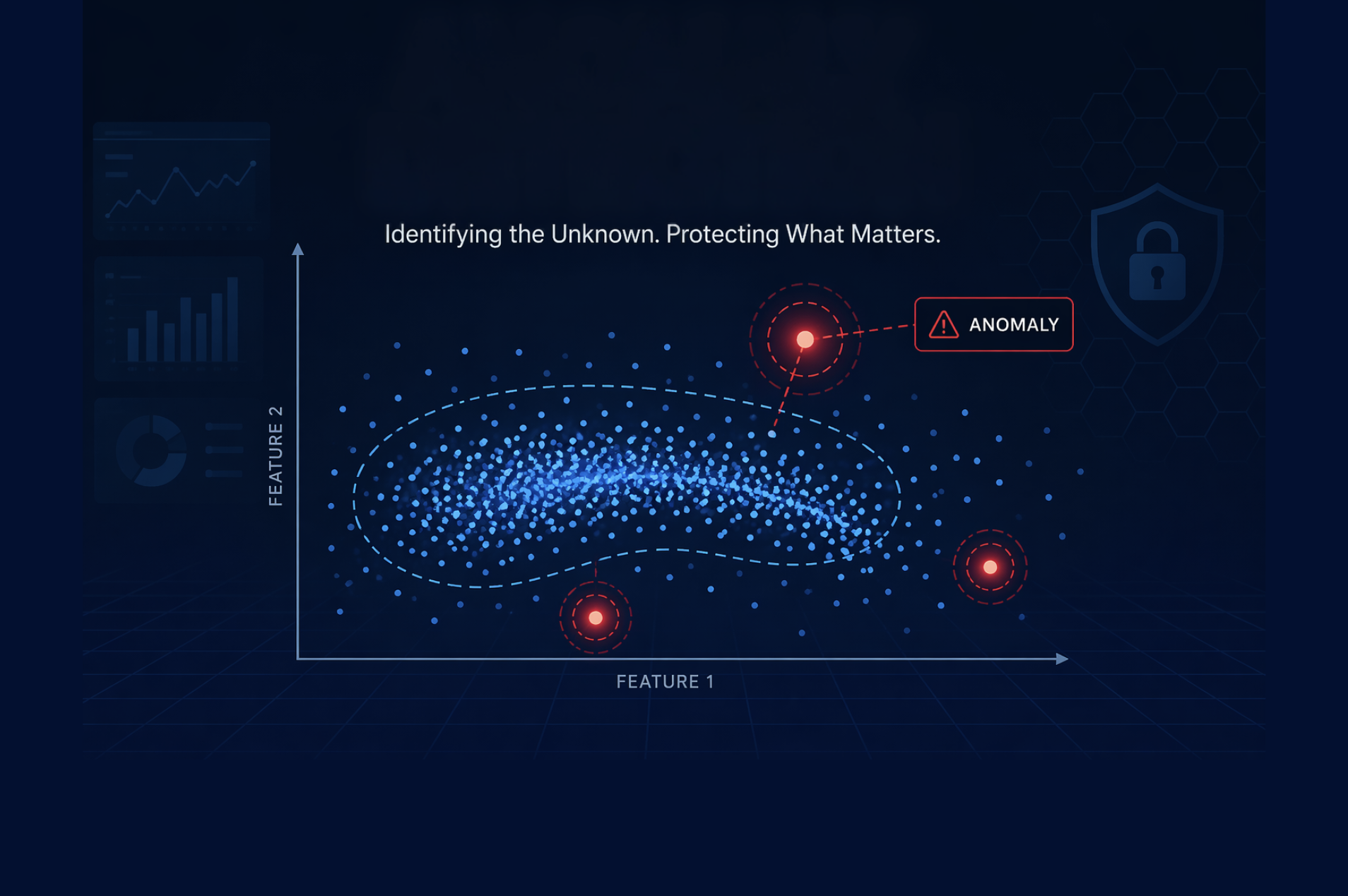
Deeply passionate about AI Security Research, I am focused on understanding and mitigating the emerging threats that AI systems introduce, delivering reliable protection across systems and infrastructure.
My goal is to bridge security operations, engineering, and AI security research to build resilient systems that protect organisations against both today’s threats and tomorrow’s emerging challenges.